Archives: All Blog Posts

Launching at Knowledge 25: Guardian AI Security Agents on ServiceNow
Blog Real-time security automation. Smarter identity governance. Unified cyber-physical GRC.
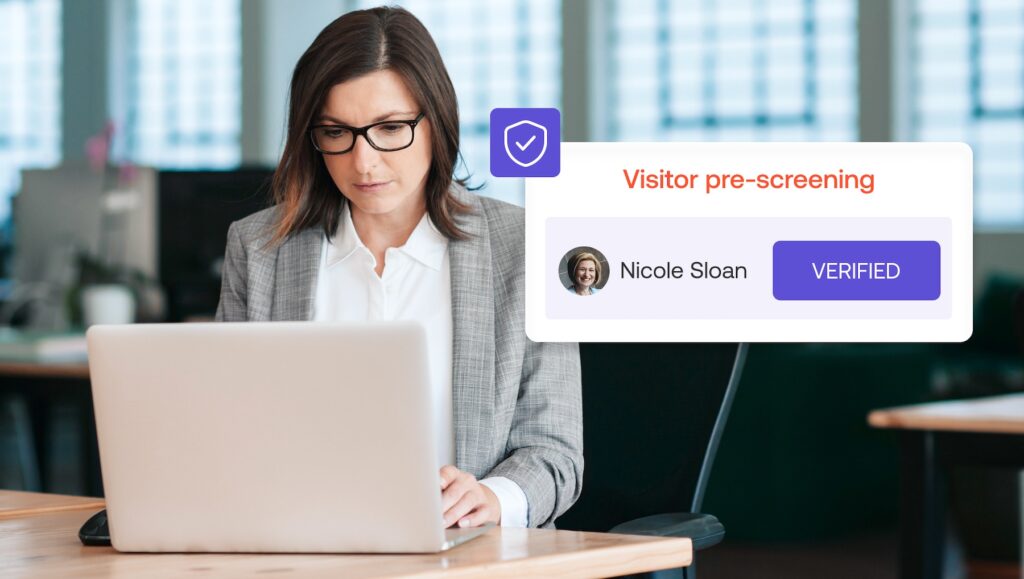
How Alert Enterprises Streamlines Visitor Management Security with Instant, Integrated Criminal Data
Blog Security isn’t just about keeping threats out; it’s about

Full Circle: Jasvir Gill Returns to RSA Innovation Sandbox as a Founding Force in Security Innovation
More than 15 years ago, Jasvir Gill took the stage

Unlock Faster, Smarter Cyber-Physical Security with the Guardian AI Security Agent
Modern businesses face new, emerging security challenges as digitization increases

Unlock the Best of Workplace Access and Visitor Management with Guardian on ServiceNow
As technology evolves and organizations grow, so do the challenges

Alert Enterprise Achieves SOC 2 Type 2 Certification
Blog Here at Alert Enterprise, we’re in the business of
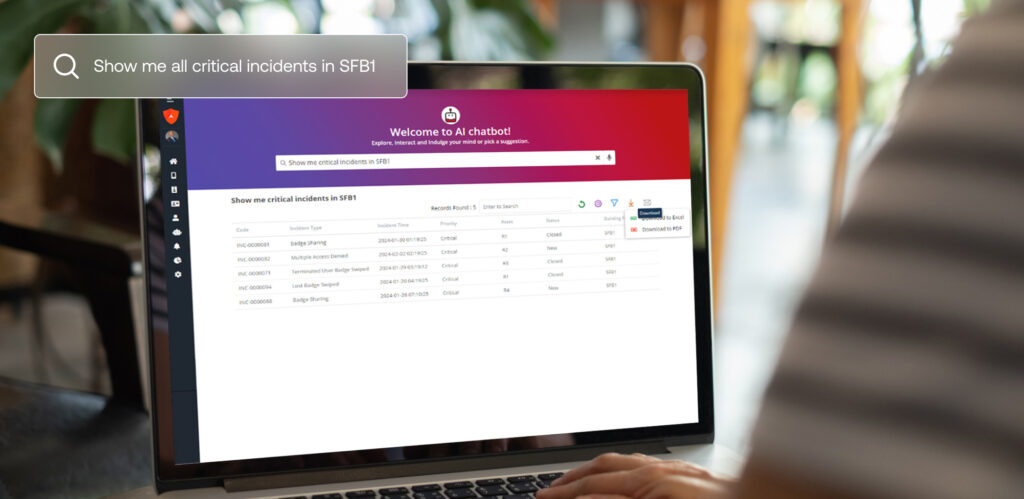
The Secret to Securing Enterprise Data While Using Generative AI? Just Ask Guardian.
Modern businesses face new, emerging security challenges as digitization increases

Guardian by Alert Enterprise: Less coffee badging, more accountability
Blog Meet John. John works for a large enterprise with
Securing the Future: How Alert Enterprise Addresses the 2025 Security Megatrends
What’s trending for 2025? Look no further than the 2025

