Blog
April 28, 2026
PIAM vs IAM vs PACS: Understanding the Difference Between Identity Management and Access Management Across Digital and Physical Security
Understand the difference between identity management and access management across IAM, PACS, and PIAM. Learn how these systems work together for end-to-end identity governance.

Overview
Why the Difference Between Identity Management and Access Management Matters More Than Ever
As organizations modernize their security architecture, many encounter three categories of identity and access technologies that sound similar but serve fundamentally different purposes: Identity and Access Management (IAM), Physical Access Control Systems (PACS), and Physical Identity and Access Management (PIAM).
Each system manages a piece of the identity and access puzzle. IAM governs digital access — who can log into which applications and systems. PACS controls physical access — which badges open which doors. But neither, on its own, provides end-to-end identity management across the full enterprise.
When a hospital terminates a clinician, the IT team may revoke their application credentials through the IAM platform while the security team forgets to deactivate their badge in the PACS.
When a contractor's project ends, their network login may expire automatically while their physical access to the building persists for weeks.
When a new employee is hired, their HR record may be created on day one, but it takes days of manual coordination before they can badge into the building or log into the systems they need.
These disconnects are not edge cases. They are the everyday reality in organizations that manage digital identity and physical access through separate, unconnected systems.
Understanding the difference between identity management and access management — and how IAM, PACS, and PIAM each address different parts of this challenge — is essential for building a unified, enterprise-grade identity governance strategy.
This guide explains what each system does, where each falls short on its own, and how they work together to close the identity and access gaps that modern organizations face.
Governs digital access to applications, cloud services, enterprise systems, and corporate networks.
Controls physical entry to buildings, facilities, and restricted areas via badges, readers, and credentials.
Governs the physical identity lifecycle — connecting HR, IAM, and PACS into a unified governance framework.
System One
What Is IAM? Identity and Access Management for Digital Resources
Identity and Access Management (IAM) is the framework of policies, processes, and technologies that govern access to an organization’s digital resources. At its core, IAM answers two questions: “Who is this person?” (identity management) and “What are they allowed to do?” (access management).
What IAM Controls
IAM platforms manage access to digital resources like applications, cloud services, enterprise systems, databases, and corporate networks. When an employee logs into the EHR system, accesses a cloud-based scheduling platform, or connects to the corporate VPN, it is the IAM system that authenticates their identity and authorizes their access.
Core IAM Capabilities
IAM platforms provide a well-established set of capabilities that have become foundational to enterprise IT security.
Authenticate once, access multiple applications without re-entering credentials. Reduces password fatigue while maintaining centralized authentication control.
Adds verification layers beyond passwords — biometric scans, hardware tokens, or one-time codes — to reduce the risk of credential-based attacks.
Governs the creation, modification, and deactivation of user accounts throughout an employee’s tenure — from hire to role change to departure.
Automates the process of granting and revoking access to specific applications and systems based on role, department, or policy.
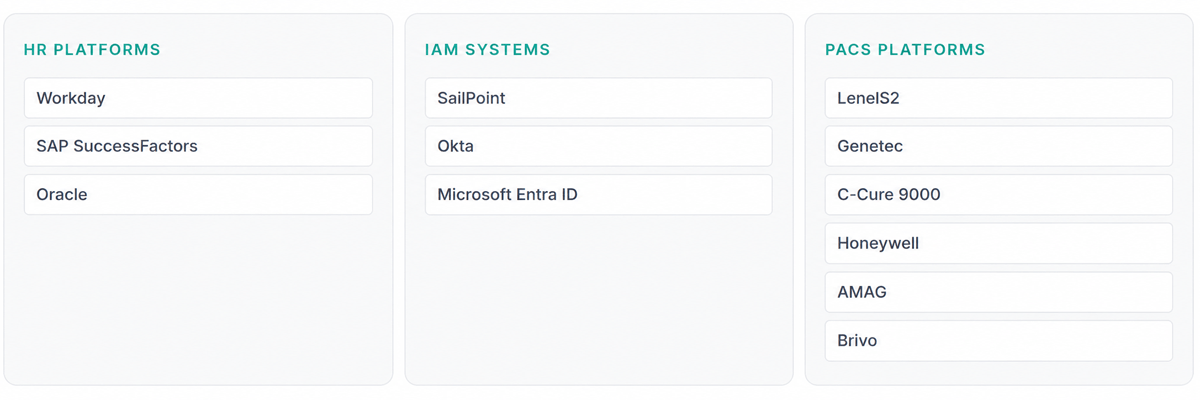
Common IAM Platforms
Enterprise IAM is a mature market with several established platforms.
The Limitation of IAM
IAM systems are powerful, but they operate exclusively in the digital domain. They manage who can log into applications. They do not manage who can walk through a physical door. An IAM platform can revoke a terminated employee’s access to the EHR system instantly — but it has no visibility into whether that same person still holds an active badge that grants them physical access to the pharmacy, the data center, or the executive suite.
System Two
What Is PACS? Physical Access Control Systems for Building Security
Physical Access Control Systems (PACS) are the hardware and software infrastructure that controls physical entry to buildings, facilities, and restricted areas. Where IAM manages digital doors, PACS manages physical ones.
What PACS Controls
PACS systems control who can physically enter a facility and which areas within that facility they can access. When an employee badges into the main entrance, swipes into a restricted lab, or uses a biometric scan to enter a secure server room, the PACS is the system making the access decision at the door.
PACS Infrastructure
Physical hardware installed at entry points that reads credentials — badge, keycard, mobile device, or biometric scanner — and communicates with the central system to determine whether access should be granted.
Issuing, activating, and deactivating the physical or digital tokens that individuals use to access controlled areas. Increasingly supports mobile credentials alongside traditional plastic badges.
Process access decisions in real time, logging every badge event and enforcing the rules configured by the security team.
Security Center — open-architecture platform unifying access control with video
The Limitation of PACS
PACS systems are essential infrastructure, but they are fundamentally access-centric, not identity-centric. They know which badge opened which door at which time. They do not know who that badge belongs to in the context of the broader organization, whether that person is still an active employee, whether their access is aligned with their current role, or whether their badge should have been deactivated three weeks ago when they transferred departments.
PACS systems control access at the door. They do not govern the identity lifecycle that determines whether that access should exist in the first place. This is the gap that PIAM is designed to close.
System Three
What Is PIAM? Physical Identity and Access Management
Physical Identity and Access Management (PIAM) is the governance layer that sits between IAM systems and PACS infrastructure — bridging the gap between digital identity management and physical access control.
Where IAM answers “who can access which applications?” and PACS answers “which badge opens which door?”, PIAM answers the higher-order question: “Based on this person’s verified identity, role, and policies, what physical access should they have — and is that access current, appropriate, and compliant?”
What PIAM Does
PIAM platforms manage the identity lifecycle for physical access and enforce governance policies across physical security systems. Rather than replacing IAM or PACS, PIAM orchestrates them — connecting HR systems, IT identity platforms, and physical access control infrastructure into a unified framework where identity drives every access decision.
This is the most effective identity access management approach for organizations that need to govern access across both digital and physical domains — because it ensures that the same identity lifecycle events (hiring, role changes, terminations) trigger consistent access changes across every connected physical system.
Core PIAM Capabilities
End-to-end identity management and automation
When a new employee is added to the HR system, the PIAM platform automatically provisions their physical access — creating their identity profile, assigning role-based access to specific facilities and areas, and issuing credentials. When they change roles, access is automatically adjusted. When they leave, access is revoked across all physical systems immediately. This is the identity lifecycle for the physical world — mirroring what IAM does for digital access but extending it to buildings, doors, and facilities.
Policy-based and persona-based access governance
PIAM platforms ensure that access decisions are driven by organizational policies — going beyond traditional role-based access control by incorporating persona-based access control principles. Access is determined not just by job title but by functional persona, including department, shift schedule, patient assignments, certification status, and operational context. Policies are defined once and enforced consistently across every facility and every PACS, regardless of the underlying hardware vendor.
PACS orchestration
A large organization may have LenelS2 at one facility, Genetec at another, and C-Cure 9000 at a third — often the result of acquisitions, phased deployments, or regional decisions. The PIAM platform operates across all of these systems through a single console, enforcing uniform policies without requiring the organization to rip and replace existing infrastructure.
Compliance reporting and access certification
Instead of manually assembling access records from multiple badge systems for a compliance audit, the PIAM platform generates comprehensive reports from a single source of truth — covering who has access to what, when access was granted or revoked, and who approved it.
Visitor and contractor identity governance
This extends the same lifecycle management to non-employee populations. Visitors are verified, screened, and issued time-bound credentials. Contractors are onboarded with role-based access tied to their engagement scope. Both are offboarded automatically when their authorization period ends.
How Guardian Delivers PIAM
Alert Enterprise Guardian is the industry-leading PIAM platform, used by Fortune 500 companies and major healthcare organizations worldwide. Guardian provides all of the capabilities described above and adds several differentiating features.
Guardian is the only platform that converges physical security, IT, and HR systems into a single, AI-powered solution. Its patented Policy-Based Access Control (PBAC) engine enforces governance policies across every connected system without custom coding.
Guardian’s Generative AI capabilities allow security teams to query identity and access data using natural language, automate incident response workflows, and receive AI-powered policy recommendations. Its cloud-based, no-code architecture enables organizations to configure workflows, forms, and notification rules without development resources — making enterprise-grade IAM systems scalable without the cost and complexity of traditional implementations.
The Full Picture
How IAM, PACS, and PIAM Work Together
A modern, enterprise-grade identity architecture does not choose between IAM, PACS, and PIAM. It requires all three, working together.
IAM
Manages digital access
Authentication and authorization for applications, cloud services, and networks.
PACS
Controls physical doors
Credentials, readers, controllers, and access rules that determine which badge opens which door.
PIAM
Governs the physical identity lifecycle
Connects HR, IAM, and PACS into a unified framework ensuring access decisions across both domains are driven by verified identity, policy, and lifecycle events.
The Bigger Picture
The Convergence of Physical and Digital Identity
The distinction between physical security and cybersecurity is collapsing. Security leaders increasingly recognize that workforce identities must be governed across both digital and physical environments — because the risks span both domains.
A compromised set of IT credentials can lead to a data breach. An active physical badge belonging to a terminated employee can lead to unauthorized facility access. But the most dangerous scenarios involve both: a former employee using a still-active badge to enter the building and a still-active login to access systems they should no longer reach.
Governs who can access applications, systems, and data. Credentials expire. Logins are revoked. But has no visibility into physical access.
Governs who can enter buildings and restricted areas. Badges are issued and revoked. But has no connection to the HR or IT identity lifecycle.
PIAM — the convergence layer
This convergence is driving the adoption of unified identity and access management governance strategies that treat physical and digital access as two expressions of the same underlying identity.
PIAM platforms are the enabling technology for this convergence. By connecting IAM and PACS through a single identity governance layer, they ensure that access policies are enforced consistently across domains, that lifecycle events propagate to all systems simultaneously, and that security teams have a unified view of every identity’s complete access profile — both physical and digital.
Guardian delivers this convergence natively. As the only platform to truly unify physical security, IT, OT, and HR systems, Guardian provides security operations automation that reduces manual processes, eliminates the gaps between siloed systems, and enables organizations to enforce consistent governance at enterprise scale.
Alert Enterprise Guardian is the leading PIAM platform built for this purpose. By unifying HR, IT, and physical security systems into a single, AI-powered framework, Guardian enables organizations to achieve true end-to-end identity management — governing every identity, every access point, and every policy from a single platform.