Blog
Security Silos are Expensive and Risky – Its Time to Shatter Them Once and for All
June 26, 2023

Our evolving digital landscape, spurred on by remote workforces, cloud technologies, and digital transformations, has birthed a new breed of cybersecurity challenges. The merging cyber and physical threats are by-products of our increasingly interconnected world. Imagine the swelling tide of the Internet of Things (IoT), projected to connect billions of devices in the coming years, igniting an exponential burst of cyber-physical risk. The advent of smart cities, autonomous vehicles, drones, and robotics marks our next frontier.
Over the past few decades, cybersecurity has undergone a profound metamorphosis, especially concerning awareness, industry vendors, security measures, and governance policies. We’ve poured resources into cutting-edge firewalls, virus/malware protections, security vulnerability scanning software, and comprehensive security programs, as well as audits and education campaigns.
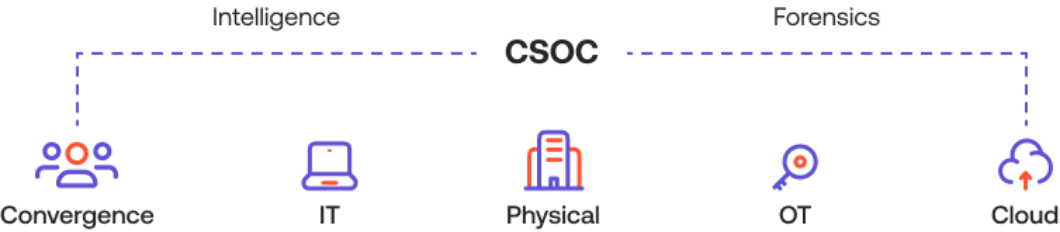
Yet, despite these advancements, we grapple with substantial blind spots – namely in physical security, access control, operational technology/SCADA, and IoT sensor devices. While these departments may have individual security protocols, they often operate in silos, thereby diminishing the overall potency of Global Security Programs.
Leading minds in the industry concur that this siloed approach to security amplifies risk, inflates costs, and cultivates a climate of regulatory mistrust, fueled by recurring breaches.
What is cementing these barriers, and how can we demolish them?
- Fear of a diminished role
Hesitation to integrate often arises from apprehensions regarding reduced roles and responsibilities.
- Physical Security is “Physical”
- As long we’re not fined, we’re good
The mantra often is, “If we’re not being fined by regulators, there’s no real issue.” Such a mindset proves detrimental, as organizations tend to resist change unless compelled.
However, let’s remember, malicious actors don’t share this view. Our upcoming model aims to illuminate how security convergence isn’t about eradicating roles, jobs, or departments, but instead about bolstering their capabilities to protect the enterprise. It’s about enhancing the workforce experience through automation, integration, and insightful data.
Converged Security Model: Empowering the Intelligent Enterprise through Digital Transformation.
The lifeblood of converged security in our digital transformation journey is people and identity. Whether employees, contractors, visitors, or temps, these individuals inhabit our facilities or connect to our corporate networks and cloud infrastructure at all hours. The goal is proper identification and assignment of roles and responsibilities.
Devices/Assets are the next pivotal elements. People need these to accomplish their daily operations and fulfill their roles and responsibilities.
Background checks and training are paramount, especially when dealing with temporary staff and contractor/service vendor personnel.
Resellers: why choose us?
Cloud Hyper Scalers, VPN, Active Directory Domains, other connected and non-connected IT & Cyber systems, Scada/PLC, and Virtual Infrastructure/machines.
Shattering the silos of security is not just necessary; it’s the way forward. It’s an invitation to step into the unknown, to innovate, and to safeguard our organizations like never before..