Protecting the modern enterprise tends to become a task of safeguarding against digital threats – and with good reason. According to the Ponemon Institute’s 2021 “Cost of Data Breach Study,” the average cost of a data breach in the United States has hit an all-time high, coming in at a cool $4.24M – up 10% from last year.
But before you write off physical security concerns forever, the study also found that 9% of incidents were rooted in a physical security breach. Servers are physical, after all, and they have to be stored somewhere – with somebody’s key.
Whether digital or physical, security events lose you time, money, and perhaps worst of all, the trust of your customers. The strongest security posture takes into account all possible angles, including physical infrastructure.
Let’s review some commonly overlooked areas that could be introducing unnecessary risk at your organization.
Silos abound in the cyber-physical world
Whether you’re working in a smart factory or boarding a plane with your phone, connected devices are shaping how we live and work. And as the workplace increasingly straddles the digital and the physical, the systems managing access to both spaces need to come together and work as one. Why? Cyber-physical attacks exploit the gaps that exist between operating systems. Factor in that many organizations operate with separate HR, OT, IT and physical security systems – and that’s a fair amount of vulnerability.
A zero-trust approach in the cyber realm, even though it’s effective, could be leaving major gaps in how you deal with physical access. By taking a zero-trust approach in the physical realm, you can implement software controls that help close gaps in terms of policy enforcement, visitors, badge deactivation and more.
Here’s the benefit(s): When you converge operational silos, you can begin linking digital and physical employee identities to create one view of access. As a result, your HR, physical security and IT teams can work from the same information to implement new policies, clarify discrepancies and respond to potential threats. Convergence also sets the stage for automating access policies – and as an added bonus, employees enjoy a smoother experience with the access they need throughout their careers.
Don’t forget about visitors …
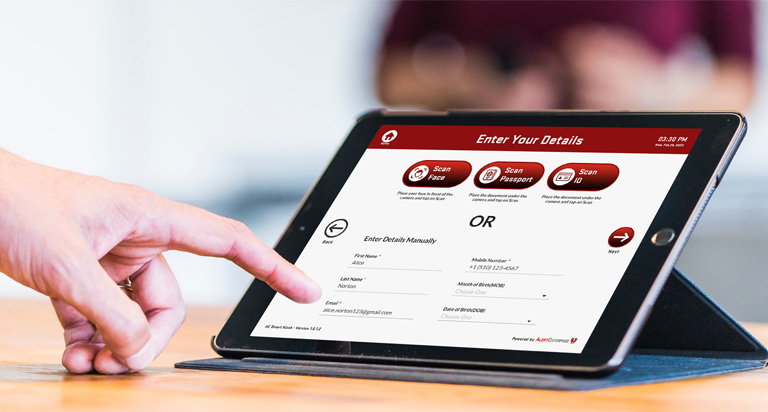
As labor shortages grow, there’s fewer available resources to mind the front desk. This is especially true in the case of hybrid work environments where employees have the freedom to set their own work hours. As a result, your visitor protocols fall on overburdened staff – or simply fall by the wayside in favor of more value-added work. An automated approach can help ensure that visitors only gain access to the right spaces once they’ve provided the appropriate credentials.
Here’s the benefit(s): When you automate visitor check-in through solutions like self-service kiosks, you’re automatically inputting that data into your overall dashboard for a complete view of everyone’s access. This comes especially in handy for organizations facing new vaccination mandates and contact tracing requirements. You’re also improving the visitor experience, which boosts your brand. You can even save extra time and money by reallocating 24/7 security guards.
… and evolving work schedules
The way we work is changing, and many companies are moving to a hybrid work format in which employees spend certain days in the office and others working remotely. As schedules become more sporadic, how will you manage physical workplace access? Since most legacy physical access control systems can only handle 24/7 card access, you will need a new strategy for making sure your physical spaces stay protected.
Here’s the benefit(s): Implementing a policy-based access management system (PBAC) for physical access helps you control the gaps between digital and physical access while maintaining visibility. And we can help: we’re currently developing the first-of-its kind policy-based access control solution.
Open new doors for your company
When you address the physical side of the security equation, you’re not just shoring up a stronger overall security posture. You will also be implementing new efficiencies that make work easier – and safer – for everyone. Let’s connect to chat about how we can help you get there using your existing system through a converged approach.
