Blog
April 13, 2026
The Ultimate Guide to Healthcare Physical Identity and Access Management (PIAM): How Modern Hospital Security Systems Work
Discover how Healthcare PIAM transforms hospital security systems. Learn how identity-driven access management improves security, compliance, and operations across health systems.

Foundation
Why the Modern Hospital Security System Must Start with Identity
Hospital security has changed fundamentally over the past decade. The traditional model — security guards at entrances, standalone camera systems, basic badge readers, and paper visitor logs — was built for a simpler time. It was designed to monitor doors and respond to incidents after they happen.
That model is no longer sufficient.
Today’s hospitals face a security landscape defined by rising workplace violence, complex identity ecosystems involving tens of thousands of employees, contractors, and visitors, regulatory frameworks that demand auditable access governance, and the convergence of physical and digital threats that require coordinated response.
A modern hospital security system must do more than control doors. It must know who is in the facility, manage where every individual can go, detect risk before incidents occur, and provide the intelligence security teams need to respond with speed and precision.
This is the role of Physical Identity and Access Management (PIAM) — a technology platform that puts identity at the center of healthcare security operations.
Alert Enterprise’s Guardian PIAM platform is purpose-built for this challenge. Unlike traditional access control, which manages badges and doors, Guardian manages the complete lifecycle of every identity that interacts with the hospital — from the moment a clinician is hired to the moment a contractor’s engagement ends, from the second a visitor checks in to the instant an emergency requires full-facility accountability. It is the only platform to converge physical security, IT, OT, and HR systems into a single, AI-powered solution with over 200 out-of-the-box integrations.
This guide explains what Healthcare PIAM is, why it matters, and how Guardian’s capabilities work together to create a hospital security system that is proactive, intelligent, and unified.
What Is PIAM
What Is Healthcare PIAM, and How Does Guardian Deliver It?
Physical Identity and Access Management (PIAM) is a security platform that automates the governance of who can access what, where, when, and why — across both physical and digital environments.
In a healthcare context, PIAM connects the systems that hospitals already rely on: HR platforms, physical access control systems (PACS), visitor management, IT identity systems, EHR platforms, and security operations tools — into a single, identity-driven framework.
Alert Enterprise’s Guardian does this by creating a unified identity profile for every person who interacts with the hospital, rather than managing each system independently. That profile becomes the foundation for every access decision, every policy enforcement action, and every security investigation. Guardian’s patented Policy-Based Access Control (PBAC) engine ensures that access policies are enforced consistently across every connected system.
At its core, Guardian provides three foundational capabilities:
Capability 01
Identity Awareness
Knowing who is in the facility. Every employee, contractor, vendor, visitor, volunteer, and student with verified, up-to-date identity information.
Capability 02
Access Governance
Controlling where each individual can go based on their verified identity, role, purpose, and policy — automatically adjusting as roles change.
Capability 03
Security Intelligence
Detecting patterns, anomalies, and risks across access systems in real time — and giving security teams the context they need to act before incidents escalate.
These three capabilities form the operating framework of a modern hospital security system.
Download the VIM + Epic Data Sheet
See how Visitor Identity Management integrates with Epic for healthcare facilities.
The Problem
Why Traditional Hospital Security Systems Fall Short
Most hospitals built their security infrastructure over many years, adding systems incrementally as needs arose. The result is a patchwork of disconnected technologies: badge systems from one vendor, visitor logs managed on paper or basic kiosks, camera systems monitored independently, and IT access credentials governed by a completely separate team.
This fragmentation creates five persistent gaps that traditional hospital security systems cannot close:
Siloed access control
Badge systems, visitor management, and IT credentials operate independently — so no single team has a complete picture of who has access to what. A terminated employee’s physical badge might be deactivated while their network login remains active.
Manual identity lifecycle management
Onboarding and offboarding involve chains of manual handoffs between HR, security, IT, and department managers. Each handoff introduces delay, inconsistency, and the risk of lingering access that should have been revoked.
Limited visitor accountability
Paper logbooks and standalone kiosks provide no real identity verification, no watchlist screening, and no visibility into visitor movement within the facility.
Reactive security posture
Without integrated data across identity and access systems, security teams respond to incidents after they occur rather than detecting risk before it escalates.
Compliance burden
When access records, visitor logs, and incident data are scattered across disconnected systems, audit preparation becomes time-consuming and error-prone.
For a deeper exploration of these challenges — including workplace violence, insider threats, emergency preparedness, and the convergence of physical and cyber risk — read our comprehensive guide: Healthcare Security Challenges: A Deep Dive.
Guardian is built to close every one of these gaps — replacing fragmented, manual approaches with automated, policy-driven governance across every identity and every access point in the hospital.
Combined, these factors create environments where incidents can escalate before security teams are even aware of them. This is the core gap that modern technology is designed to close.
Core Capabilities
Core Capabilities of Guardian PIAM for Healthcare
Guardian offers an integrated set of capabilities that work together to create a unified hospital security system. The following sections detail each capability and its role in healthcare security.
01
Visitor identity management
Pre-registration, ID verification, watchlist screening, EHR-integrated patient matching, digital credentials.
02
Workforce Identity & Access
Automated lifecycle from hire to termination — role-based provisioning, instant revocation, self-service portals.
03
Contractor & Vendor Governance
Time-bound access, certification tracking, automatic revocation post-engagement.
04
IT & Physical Convergence
Single identity lifecycle governing both physical badges and digital credentials — across all connected systems simultaneously.
05
Mobile Credentials
Apple Wallet, Google Wallet, Samsung Wallet — replacing legacy badges with instant digital provisioning and revocation.
06
Asset Governance
Physical assets linked to verified identities — chain of custody, return workflows, complete audit trails.
07
SOC Intelligence
AI-powered anomaly detection, natural language queries, identity-correlated alerts, proactive risk detection.
08
Emergency Mustering
Real-time headcount accountability, mass notification, automated zone lockdown — built on daily identity data.
09
Analytics & Reporting
Centralized compliance reporting for HIPAA, Joint Commission, CMS, OSHA — configurable dashboards, unified audit trails.
Visitor Identity Management
Hospitals receive thousands of visitors every day — family members, caregivers, contractors, vendors, volunteers, students, delivery personnel, and external clinicians. Managing this volume without automated identity verification creates significant security and operational risks.
Guardian’s Visitor Identity Management (VIM) transforms visitor management from a basic check-in process into a comprehensive identity governance capability, fully integrated with the same platform that governs workforce access.
VIM begins before the visitor arrives. Pre-registration workflows allow hospital staff or patients to register expected visitors in advance, providing identity information that can be verified and screened before the visit.
Upon arrival, visitors verify their identity through government ID scanning, identity matching, or biometric verification. Guardian automatically screens visitors against security databases including sex offender registries, internal watchlists, and banned visitor lists, and enforces hospital-specific visitor policies.
In healthcare environments, visitor-to-patient matching is particularly critical. Guardian integrates with the hospital’s Electronic Health Records (EHR) platform — such as Epic, Meditech, or Oracle Health — using healthcare messaging standards like HL7 to verify that visitors are authorized to visit specific patients.
After verification and screening, visitors receive digital or physical credentials with clearly defined access parameters: authorized areas, time restrictions, and host information. Security teams can monitor active visitors in real time through Guardian’s centralized dashboards, and the system generates automated compliance reports for audit purposes.
Pre-registration
Identity submitted before arrival
ID verification
Government ID, biometric matching
Watchlist screening
Sex offender registries, internal lists
EHR patient matching
HL7 integration with Epic, Meditech
Digital credential
Time-bound, area-restricted access
The result is a visitor management process that is faster for visitors, more secure for the hospital, and fully auditable for compliance.
Workforce Identity and Access Management
Healthcare organizations manage extraordinarily complex identity ecosystems. A large health system may have tens of thousands of active identities at any time: full-time employees, part-time clinicians, rotating residents and fellows, traveling nurses, administrative staff, facilities teams, and executive leadership. Each person requires access to specific areas based on their role, department, shift, and clinical responsibilities.
Guardian automates the entire workforce identity lifecycle, from hire to role change to termination.
When a new clinician is onboarded through the hospital’s HR system, Guardian automatically creates their identity profile, provisions role-based physical access (badge credentials for their assigned areas), and triggers any required training or credential verification — without manual intervention from security teams.
When that clinician transfers to a different department, Guardian automatically adjusts their access permissions to reflect their new role — removing access to areas they no longer need and granting access to areas their new role requires.
When an employee leaves the organization, Guardian immediately revokes all access — physical badge credentials, IT system logins, and any other entitlements across every connected system.
Guardian also includes self-service portals where employees can request additional access, update their credentials, or report issues — reducing the administrative burden on security and IT teams while maintaining policy-driven approval workflows. The platform’s no-code configurability means hospitals can customize forms, workflows, and notification rules without development resources.
Contractor and Vendor Access Governance
Hospitals depend on a large external workforce — contractors performing facility maintenance, IT service providers, medical equipment technicians, construction crews, food service operators, and specialized clinical consultants. These individuals often require access to multiple areas, sometimes including sensitive clinical environments.
Without integrated access governance, contractor management becomes an uncontrolled risk. Badges are issued at the front desk with minimal verification. Access permissions are not time-bound. Credentials persist long after work is completed.
Guardian extends identity lifecycle governance to the entire non-employee population. Contractors and vendors are onboarded through a dedicated portal that captures identity information, verifies credentials and certifications, validates background checks, and provisions access based on the scope and duration of their engagement.
Access is automatically time-bound, tied to the contract period, and can be further restricted by time of day, specific buildings, or designated work zones. When the engagement ends, access is revoked automatically across all systems.
The platform also supports ongoing compliance management for external workers, including training verification, certification expiration tracking, and periodic access reviews — ensuring that contractor access is governed with the same rigor as employee access throughout the engagement lifecycle.
IT and Physical Access Convergence
One of the most significant gaps in traditional hospital security is the separation between physical access and IT access. A clinician’s badge access to the maternity ward is managed by the security department, while their login credentials for EHR systems, pharmacy applications, and clinical databases are managed by IT. These two domains rarely communicate.
Guardian solves this by governing both physical and IT access through a single identity lifecycle. Access is provisioned, modified, and revoked across both domains simultaneously, driven by the same HR events and the same policy engine. Guardian is the only platform to truly converge physical security, IT, and OT systems — closing the gap that traditional, siloed approaches leave wide open.
This convergence also simplifies compliance. Frameworks like HIPAA, HITRUST, and Joint Commission standards increasingly require organizations to demonstrate unified access governance across both physical and digital systems.
Guardian integrates with IT identity providers and IAM systems — such as ServiceNow, Okta, Active Directory, and SailPoint — to create a seamless, converged access governance framework that covers every door and every application.
Siloed approach
- Physical badges managed by security, IT credentials managed separately — two teams, two systems
- Employee leaves: badge deactivated, network login persists — or vice versa
- Separate compliance reporting for physical and digital access — fragmented audit trail
Guardian converged approach
- Single identity lifecycle — physical and digital access provisioned and revoked simultaneously
- Immediate revocation across all systems — every door and every application, at once
- Unified compliance history — HIPAA, HITRUST, Joint Commission coverage across both domains
Mobile Credentials and Digital Access
Traditional plastic badge systems are expensive to produce, easy to lose, and difficult to manage at scale — especially across large, multi-facility health systems. When a badge is lost or stolen, it represents both a security risk and an operational disruption.
Guardian supports mobile credentials that replace physical badges with digital alternatives stored in Apple Wallet, Google Wallet, or Samsung Wallet. Through partnerships with HID, Wavelynx, Safetrust, LEGIC, and Gantner, Guardian enables employees to securely access doors, parking structures, elevators, and other controlled areas with a tap of their smartphone or smartwatch.
Mobile credentials through Guardian offer several advantages for healthcare security. Provisioning and revocation happen instantly. A new hire receives their credential digitally on day one, and a departing employee’s credential is disabled immediately. Lost or stolen devices can be remotely deactivated without the need to reissue physical badges. And mobile credentials are fully integrated with Guardian’s policy engine, so access rights are always current with the employee’s identity profile.
For healthcare organizations managing thousands of credentials across multiple facilities, mobile credentialing reduces cost, accelerates onboarding, and strengthens security simultaneously.
Asset Governance
Hospital security extends beyond people to the physical assets they use: keys, laptops, mobile devices, company vehicles, access cards, and other equipment that must be tracked from assignment to return.
Guardian includes asset governance capabilities that link physical assets to verified identities. When an asset is assigned to an employee or contractor, Guardian records the chain of custody. When the individual transfers roles or leaves the organization, Guardian triggers return workflows and flags any unreturned assets.
Guardian’s self-service portals allow employees to request replacement equipment or report missing items, with configurable approval workflows that ensure proper authorization and documentation. Complete asset inventory and audit trails are maintained on a single dashboard, supporting compliance requirements and reducing the risk of unaccounted equipment.
Security Operations Center (SOC) Intelligence
The true power of Guardian emerges when identity and access data is connected to security operations.
Guardian SOC Insights does not just monitor cameras and alarms — it correlates identity data, access events, behavioral patterns, and security signals across the entire hospital to detect risk in real time.
When a badge is used at an unusual time, Guardian SOC Insights can immediately surface who the badge belongs to, what their role is, whether they are authorized for that area at that hour, and whether their access pattern is consistent with previous behavior. When a visitor triggers a watchlist match, the SOC receives an instant alert with full identity context. When repeated access-denied events occur at a restricted area, the SOC can investigate with a complete profile of the individual involved.
This intelligence-driven approach transforms security operations from reactive alarm management to proactive risk detection. SOC teams can identify emerging threats before they become incidents, respond to alerts with full contextual awareness, and investigate incidents with complete audit trails across all connected systems.
Guardian’s AI-powered analytics further enhance SOC capabilities by detecting anomalies that human operators might miss — badge swipes at off-shift hours, piggybacking patterns, unusual movement across facilities, or access attempts that deviate from established behavioral baselines. Generative AI capabilities allow security teams to query Guardian using natural language — asking questions like “show me all after-hours access to the pharmacy this week” — and receive instant, actionable intelligence.
Generative AI allows security teams to query Guardian using natural language and receive instant, actionable intelligence — no analyst required.
Emergency Mustering and Crisis Response
When an emergency strikes — fire, active shooter, natural disaster, chemical hazard, or mass casualty event — hospitals must account for every person in the facility. Unlike other organizations, hospitals cannot simply evacuate everyone. Patients may be immobile, connected to life support, or in the middle of surgical procedures. Staff must be coordinated across clinical teams, security, and administration.
Guardian’s Emergency Mustering capability leverages the same identity and access data used for daily security governance to know exactly who is in the building at any given moment — and to verify that everyone has been accounted for during an evacuation or shelter-in-place event.
Because Guardian already maintains real-time identity awareness across all connected systems, emergency mustering does not require a separate data source or a parallel process. The platform uses existing badge activity, visitor check-in records, and access events to provide real-time headcount visibility. Security and emergency teams can identify individuals who may need assistance, coordinate movement to designated assembly points, and verify accountability with precision rather than relying on manual roll calls.
Guardian’s mass notification capabilities ensure that instructions reach the right people at the right time through mobile alerts, overhead systems, and direct integration with security operations. When paired with Guardian’s access control infrastructure, the platform can also automatically lock down specific zones, redirect traffic flow, and provide incident commanders with real-time situational awareness.
Emergency preparedness is not a once-a-year drill. It is a continuous operational capability that the PIAM platform supports every day through the same identity and access data it uses for routine security governance.
Healthcare Security Analytics and Reporting
Healthcare organizations face demanding compliance and reporting requirements from multiple regulatory bodies — The Joint Commission, CMS Conditions of Participation, OSHA, HIPAA, HITRUST, and state-level security mandates.
When access records, visitor logs, incident data, and compliance evidence are scattered across disconnected systems, preparing for audits is time-consuming and error-prone.
Guardian centralizes all identity, access, and security data into a single reporting framework. Automated reports can be generated for periodic reviews covering active identities, pending approvals, training compliance, access certifications, visitor activity, and incident history.
Guardian’s analytics capabilities go beyond compliance reporting. Security leaders can use configurable dashboards to analyze access trends, identify high-risk areas, measure policy enforcement effectiveness, and track key performance indicators across the entire security program. The platform integrates with IT, HR, cybersecurity, learning management, and ticket management systems to generate reports that provide a unified view of risk across the enterprise.
Integration
How Guardian Integrates with Existing Hospital Systems
One of the most critical factors in evaluating a hospital security system is how well it integrates with the infrastructure the hospital already has in place. Hospitals cannot rip and replace their existing technology stack. Guardian is designed to work with — and enhance — the systems that are already deployed, through over 200 out-of-the-box connectors that require no custom coding.
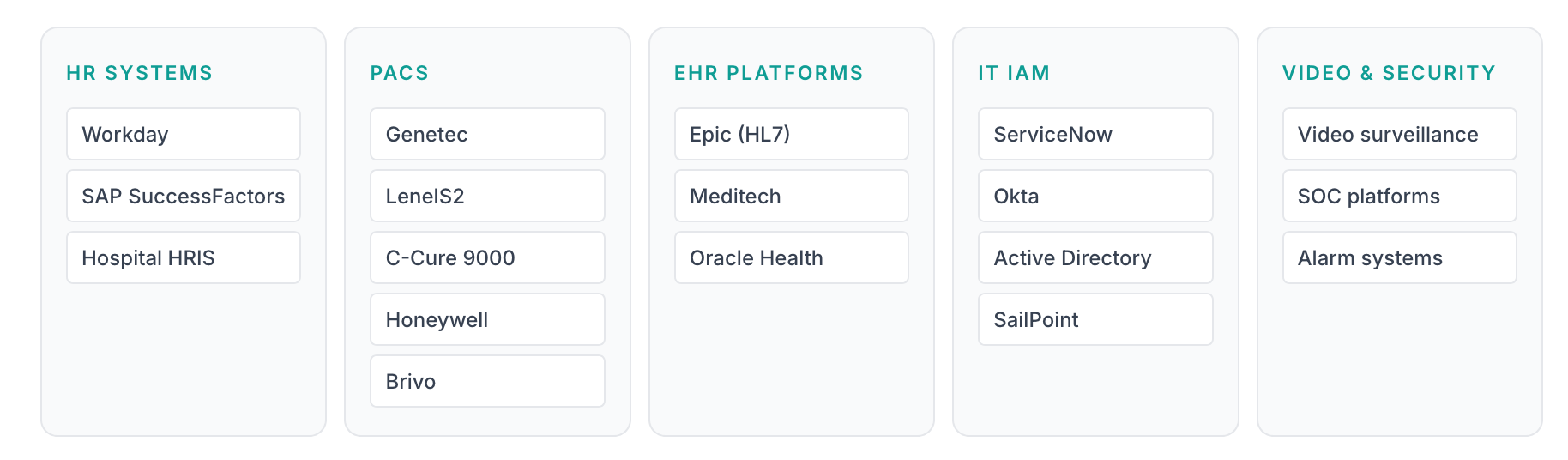
The breadth and depth of these integrations is what distinguishes Guardian from standalone access control or visitor management systems. It is the only platform that converges physical security, IT, OT, and HR systems into a single, AI-powered solution — no coding or customization required.
Enterprise Scale
Enterprise PIAM: Managing Security Across Multi-Facility Health Systems
Large healthcare organizations operate dozens or even hundreds of facilities — including hospitals, outpatient clinics, surgery centers, administrative offices, and research facilities. Each location may have different physical access control systems, different visitor policies, and different security teams.
Without a centralized platform, maintaining consistent security policies across this distributed environment is nearly impossible. Each facility operates as its own security silo, with its own processes, its own data, and its own blind spots.
Guardian solves this by providing a single, unified console that governs identity and access across every facility in the health system. Its cloud-based, multi-tenant architecture is designed specifically for complex, distributed environments. Policies are defined once and enforced everywhere. Identity data is centralized and accessible to security teams across all locations. Reporting and compliance evidence spans the entire organization rather than individual sites.
Guardian — Single Unified Console
Hospital campuses
Outpatient clinics
Surgery centers
Administrative offices
Research facilities
Multiple PACS vendors
Remote locations
Newly acquired sites
Guardian’s highly configurable platform supports drag-and-drop workflow configuration, customizable forms, and facility-specific policy rules — all without coding — so that individual hospitals can adapt to local requirements while operating within a consistent enterprise governance framework.
This enterprise approach enables healthcare organizations to standardize access policies and visitor workflows across all facilities, centralize identity data and security reporting for system-wide visibility, ensure consistent security governance regardless of which PACS vendor or badge system each facility uses, and scale security operations efficiently as the health system grows through acquisitions, new construction, or service expansion.
For healthcare organizations managing complex, multi-site environments, enterprise PIAM is not a luxury — it is a requirement for maintaining consistent, auditable security governance at scale.
Operational Impact
The Impact of PIAM on Healthcare Operations
Healthcare PIAM is often evaluated as a security investment, but its impact extends well beyond the security department.
Efficiency
Faster onboarding
New hires receive credentials and access rights on day one — no waiting days or weeks for badge provisioning.
Productivity
Reduced administrative burden
Self-service portals and automated workflows free security and IT teams for higher-value work.
Experience
Better patient & visitor experience
Streamlined check-in, pre-registration, and digital credentials create a welcoming arrival without sacrificing security.
Compliance
Stronger compliance posture
Centralized reporting and continuous policy enforcement reduce audit preparation effort across HIPAA, Joint Commission, HITRUST, and more.
Cost
Cost reduction
Eliminating manual processes, reducing badge costs through mobile credentialing, and consolidating platforms all deliver measurable savings.
Risk
Proactive risk detection
AI-powered analytics detect emerging threats before incidents occur — turning security from reactive to preventive.
Implementation
Best Practices for Implementing Healthcare PIAM
Healthcare organizations planning to implement a PIAM platform should consider several best practices to ensure successful deployment and adoption.
01
Start with identity governance
Before selecting technology, define the identity lifecycle processes the platform must support. Map how employees, contractors, and visitors are onboarded, managed, and offboarded today — and identify the gaps, delays, and inconsistencies the PIAM platform must eliminate.
02
Standardize policies before automating
A PIAM platform enforces the policies you define. Standardize visitor policies, access approval workflows, badge issuance procedures, and revocation protocols across facilities before implementing automation.
03
Prioritize integration
The value of a PIAM platform scales with the number of systems it connects. Prioritize integration with core systems first — HR, PACS, and visitor management — then expand to IT identity systems, EHR platforms, video surveillance, and SOC tools.
04
Leverage cloud deployment
Cloud-based PIAM platforms offer faster deployment, lower infrastructure costs, and easier scalability. For multi-facility health systems, cloud deployment simplifies centralized management and ensures all locations operate on the same platform version.
05
Train staff and security teams
Technology adoption depends on user readiness. Security teams, front-desk staff, department administrators, and facility managers all interact with the PIAM platform differently. Training programs should be role-specific and ongoing.
06
Measure and iterate
Define key performance indicators — average onboarding time, badge revocation latency, visitor throughput, compliance audit scores, and incident response time — and use the platform’s analytics to track and improve performance continuously.
What's Next
The Future of Healthcare Security Technology
Healthcare security technology is evolving rapidly, and PIAM platforms are at the center of that evolution. Several emerging trends will shape the next generation of hospital security systems.
AI-powered predictive risk scoring
Moving beyond anomaly detection to identifying individuals, access patterns, and environmental conditions that indicate emerging threats — before any incident occurs.
Generative AI for security teams
Natural-language queries, automated report generation, and AI-powered policy recommendations that accelerate decision-making across the entire security program.
Mobile-first credentialing as default
Legacy badge systems replaced with digital credentials that are more secure, easier to manage, and less costly to operate — especially at scale across multi-facility health systems.
Converged physical-cyber security
Physical access and digital access treated as two sides of the same identity governance challenge — eliminating the gaps that fragmented approaches create and that threat actors exploit.
These trends all point in the same direction: toward an identity-driven, AI-powered, fully integrated hospital security system that provides complete visibility, automated governance, and proactive intelligence across every facility, every identity, and every access point.
Conclusion
Identity Is the Foundation of Modern Hospital Security
The security challenges facing hospitals today — workplace violence, unauthorized access, insider threats, regulatory compliance, emergency preparedness, and the convergence of physical and cyber risk — cannot be solved by adding more cameras, more badges, or more guards.
They can only be solved by putting identity at the center of every security decision.
As this guide has detailed, Alert Enterprise Guardian provides the unified foundation that makes this possible. From automated workforce lifecycle management and EHR-integrated visitor identity verification to converged IT-physical access governance, AI-powered SOC intelligence, and real-time emergency mustering, Guardian connects every capability into a single platform that knows every identity, governs every access point, detects every risk signal, and responds with the speed and precision that healthcare environments demand.
The result is a hospital security system built not on fragmented tools, but on a single, identity-driven operating framework that protects healthcare workers, improves patient safety, strengthens operational resilience, and positions the organization for the evolving threats of 2026 and beyond.
Ready to move from exposure to control?
See how Alert Enterprise Guardian unifies visitor management, workforce access governance, and real-time security intelligence into one healthcare-focused platform.