Blog
April 10, 2026
Healthcare Security Challenges: A Deep Dive into the Risks Hospitals Face
From workplace violence and unauthorized access to emergency preparedness — how identity-driven technology is solving the most complex security problems in modern healthcare.
Overview
Why Healthcare Security Is One of the Most Complex Operational Challenges in Modern Hospitals
Healthcare security has become one of the most complex operational challenges hospitals face today. Hospitals must protect patients, clinicians, visitors, medical equipment, and sensitive areas, while maintaining an open and welcoming care environment.
This is not a standard enterprise security problem.
Hospitals operate 24 hours a day, 365 days a year. They serve emotionally distressed patients, grieving families, individuals in mental health crises, and thousands of contractors and vendors who require access to clinical and operational areas.
They house controlled substances, high-value medical equipment, and some of the most sensitive personal data any organization holds.
Modern healthcare security strategies must balance three priorities simultaneously:
- Protecting patients and care teams from physical harm
- Maintaining efficient hospital operations without security becoming a barrier to care
- Ensuring compliance and risk governance across complex regulatory frameworks
Protect patients & care teams from physical harm
Every person in the facility — patient, visitor, clinician — must be kept safe at all times.
Maintain efficient hospital operations
Security must never become a barrier to care delivery or clinical workflow.
Ensure compliance & risk governance
Joint Commission, OSHA, HIPAA, CMS — governance must be continuous, not reactive.
Traditional hospital security systems built on disconnected badge systems, paper visitor logs, standalone security cameras, and manual access processes are no longer sufficient. These fragmented approaches limit visibility, create operational inefficiencies, and leave critical gaps that bad actors and unforeseen events can exploit.
Today’s leading healthcare organizations are shifting toward identity-driven security platforms that unify visitor management, workforce access governance, and security intelligence into a single operational framework.
This guide explains the full scope of security challenges facing hospitals today and how modern technology strategies are closing the gaps that traditional approaches leave open.
Download the VIM + Epic Data Sheet
See how Visitor Identity Management integrates with Epic for healthcare facilities.
The Full Scope
The Unique Security Challenges in Healthcare
Healthcare environments differ significantly from corporate offices, manufacturing facilities, or retail operations. The nature of care delivery itself creates a uniquely challenging security landscape.
Hospitals must remain accessible to patients, families, emergency responders, clinicians, students, contractors, vendors, and volunteers around the clock. Unlike a corporate campus where access can be strictly controlled, hospitals are fundamentally open environments serving diverse, unpredictable populations.
Security teams must manage a wide and overlapping range of risks.
Workplace Violence
Workplace violence has become one of the most urgent and costly security challenges in healthcare. Healthcare workers are roughly five times more likely to experience workplace violence than employees in any other industry. According to the American Hospital Association’s 2025 landmark study, the total annual cost of violence to U.S. hospitals is estimated at $18.27 billion, a figure that encompasses both prevention investments and post-incident costs.
Today’s leading healthcare organizations are shifting toward identity-driven security platforms that unify visitor management, workforce access governance, and security intelligence into a single operational framework.
This guide explains the full scope of security challenges facing hospitals today and how modern technology strategies are closing the gaps that traditional approaches leave open.
$18.27B
The problem is not confined to isolated, extreme events. Nurses, physicians, front-desk staff, and security officers routinely face verbal abuse, physical aggression, threats, and intimidation from patients, visitors, and occasionally colleagues. Emergency departments, behavioral health units, and maternity wards are especially high-risk environments where emotional volatility is part of the operational reality.
What makes this challenge particularly complex for security teams is that the sources of violence are varied and often unpredictable. Patients in distress, family members under emotional strain, individuals experiencing mental health crises, and even unauthorized individuals who gain access to clinical areas can all become sources of risk. Staff burnout and workforce shortages compound the problem. Stressed, understaffed teams are less equipped to de-escalate volatile situations and more likely to experience the consequences of violence firsthand.
Nearly two in five healthcare workers have considered leaving their positions due to safety concerns. When 40 percent of a hospital’s workforce is questioning whether they feel safe enough to stay, workplace violence stops being a security line item and becomes a retention crisis that directly threatens care quality.
When 40% of a hospital’s workforce questions whether they feel safe enough to stay, workplace violence stops being a security line item and becomes a retention crisis that directly threatens care quality.
Technology-driven strategies are now central to mitigating workplace violence risk, including identity verification for all visitors, controlled access to sensitive units, behavioral analytics and pattern detection, and integrated security operations center (SOC) intelligence that enables early intervention. To dive deeper into how technology can prevent workplace violence, read our in-depth guide.
Unauthorized Access to Facilities and Sensitive Areas
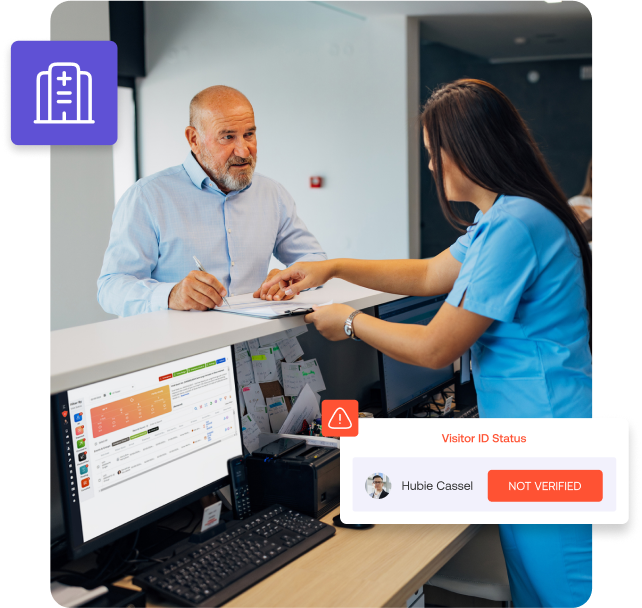
Unauthorized access remains one of the most persistent and fundamental healthcare security risks. The 2026 State of Physical Security Report found that unauthorized entrances were among the top five security incidents that increased in hospitals during 2025.
Hospitals contain numerous sensitive areas that require strict access control, including emergency departments, intensive care units, pharmacies and medication storage areas, maternity and neonatal wards, laboratories, psychiatric units, and data centers.
Each of these zones carries different risk profiles and requires different levels of access restriction. A visitor who accidentally wanders into a pharmacy presents a different type of risk than a former employee who retains active badge credentials, but both represent failures in access governance.
Emergency Departments
Intensive Care Units
Pharmacies & Medication Storage
Maternity & Neonatal Wards
Laboratories
Psychiatric Units
Data Centers
Operating Rooms
The challenge is compounded by the sheer volume and diversity of people moving through hospitals daily. A single large hospital may process thousands of visitors, hundreds of contractors and vendors, rotating clinical staff across multiple shifts, students and trainees, and emergency responders, all within a 24-hour period. Without a centralized visitor management system, hospitals cannot consistently enforce who is allowed where, when, and for what purpose.
Identity-driven access control allows hospitals to enforce policies that restrict entry based on verified identity, role, time of day, and operational need. When access is tied to identity rather than simply a badge or a key, hospitals can reduce exposure of staff to unknown individuals, limit escalation risk in sensitive environments, and create predictable, manageable care areas where clinicians can focus on patients rather than potential threats.
Insider Threats and Internal Access Risk
Not all security threats come from outside the facility. Insider threats from employees, contractors, or vendors who misuse access privileges or violate policies, represent a significant and often underestimated risk in healthcare environments.
Hospitals manage thousands of active identities at any given time: full-time employees, part-time clinicians, rotating residents, contractors performing facility maintenance, vendors servicing medical equipment, and volunteers. These identities are often managed through different systems with different processes, creating inconsistencies in how access is provisioned, monitored, and revoked.
Manual access management processes commonly lead to excessive permissions that accumulate over time as employees change roles, delayed revocation when individuals leave or are terminated, and inconsistent policy enforcement across departments and locations.
The consequences are tangible. An employee who changes departments may retain access to their previous unit long after they should. A contractor whose engagement ended three months ago may still hold an active badge. These gaps are not theoretical, they are operational realities in hospitals that rely on manual processes to govern internal access.
Traditional Manual Approach
- Permissions accumulate over time as employees change roles
- Revocation delayed when individuals leave or are terminated
- Inconsistent enforcement across departments and locations
- Separate systems for contractors, employees, vendors
PIAM Automated Approach
- Permissions accumulate over time as employees change roles
- Access revoked immediately across all systems when roles change
- Provisioned based on verified role, auditable for compliance
- Single integrated identity lifecycle across all identity types
Workplace access systems directly address this challenge by automating the lifecycle of access privileges. PIAM platforms integrate with HR systems, credentialing databases, and access control infrastructure to ensure that access is provisioned based on role, continuously aligned with current responsibilities, revoked immediately when roles change or engagements end, and auditable for compliance purposes.
PIAM ensures that internal access is governed with the same rigor as external entry — closing one of the most critical and commonly overlooked gaps in healthcare security.
Identity-driven access control allows hospitals to enforce policies that restrict entry based on verified identity, role, time of day, and operational need. When access is tied to identity rather than simply a badge or a key, hospitals can reduce exposure of staff to unknown individuals, limit escalation risk in sensitive environments, and create predictable, manageable care areas where clinicians can focus on patients rather than potential threats.
Medical Equipment and Pharmaceutical Theft
Healthcare facilities are not just places of care, they are home to millions of dollars’ worth of medical equipment, pharmaceutical products, and sensitive clinical assets. This makes them attractive targets for theft from both external actors and, critically, from insiders.
The ongoing opioid crisis has intensified the risk around controlled substance security. Hospitals, pharmacies, and medication storage areas are targeted not only by outsiders but also by staff members with direct access. High-value diagnostic equipment, surgical instruments, and portable medical devices are similarly vulnerable, especially in large campuses with multiple buildings and distributed storage locations.
The challenge is that traditional inventory management and perimeter security measures treat asset tracking and identity management as separate problems. Hospitals may know that a piece of equipment is missing, but they cannot connect that loss to a specific individual, access event, or pattern of behavior. Spreadsheets, manual sign-out logs, and disconnected inventory systems create blind spots where theft and diversion go undetected, sometimes for weeks or months.
This is where asset governance becomes critical.
An effective asset governance platform connects physical assets directly to verified identities so hospitals always know who has which piece of equipment, when it was assigned, and whether it has been returned. Rather than treating asset tracking as a standalone inventory exercise, asset governance embeds it into the broader identity and access lifecycle.
Moreover, without real-time tracking, behavioral analytics, and identity-correlated access monitoring, hospitals struggle to detect theft before it escalates or to identify patterns that indicate a developing problem.
Modern security analytics platforms help hospitals address this by analyzing access patterns and behavioral indicators across systems. Repeated access to medication storage areas outside normal hours, unusual badge usage patterns, and movement anomalies can all signal potential theft or diversion risks, and can be flagged for investigation before incidents occur.
Large Facilities, Complex Campuses, and High Traffic
The physical scale of modern hospitals creates security challenges that are fundamentally different from those in smaller or more contained facilities. A large medical campus may span multiple buildings, include above-ground and underground walkways, operate parking structures, house research facilities alongside clinical areas, and serve as a training site for medical students and residents.
The result is an enormous number of access points, movement paths, and monitoring zones, many of which are difficult for security teams to cover with traditional guard patrols and fixed-camera surveillance. High-traffic environments also create operational noise that makes it harder to distinguish between normal activity and suspicious behavior.
Without centralized systems that correlate identity data with access events and movement patterns across the entire campus, security teams are left with fragmented visibility. They may know that a badge was used at a particular door, but they may not know who used it, whether the person was authorized, or whether their movement pattern is consistent with their role.
Without integrated platforms
Badge used at a door — but security can't confirm who used it, whether they were authorized, or if the movement pattern matches their role. Visibility is siloed per system.
With integrated platforms
Access control, visitor management, workforce identity, and surveillance connect into a single operational picture — enabling real-time anomaly detection across the entire campus.
Integrated security platforms address this by connecting access control, visitor management, workforce identity systems, and surveillance infrastructure into a single operational picture, allowing security teams to monitor activity across facilities in real time, detect anomalies that span multiple systems, and respond with full context rather than partial information.
Staffing Shortages and Security Workforce Challenges
The healthcare staffing shortage does not stop at the clinical workforce, it extends directly to hospital security teams. Security departments are often understaffed, which limits their ability to patrol large facilities, respond to incidents promptly, and maintain the level of presence that deters aggressive behavior.
At the same time, clinical staffing shortages increase the overall risk environment. When nursing units are stretched thin, patients experience longer wait times and reduced attention. Family members become more frustrated. Emotional volatility rises. And the security incidents that result from these conditions fall on a security team that is equally stretched.
This creates a compounding problem: the conditions that generate security risk are the same conditions that reduce the organization’s capacity to respond to it.
Technology is not a replacement for trained security professionals, but it is a force multiplier. Cloud-based monitoring platforms, AI-assisted video analytics, automated visitor management, and centralized access governance allow smaller security teams to maintain broader visibility, prioritize response based on risk severity, and focus their limited personnel on the situations that require human judgment and intervention.
Emergency Preparedness and Crisis Response
Hospitals must be prepared for a wide range of emergency scenarios including fires, natural disasters, active shooter events, chemical or biological hazards, power outages, and mass casualty incidents. Unlike most other facilities, hospitals cannot simply evacuate and regroup. They must maintain continuity of care for patients who may be immobile, unconscious, connected to life-support equipment, or in the middle of surgical procedures.
This makes emergency preparedness in healthcare uniquely complex. Evacuation plans must account for patients with varying levels of mobility and medical dependency. Staff must know exactly who is in the building, where they are, and what resources are available to move them safely. Communication must be coordinated across clinical teams, security, administration, and external emergency responders often simultaneously.
Despite the critical nature of this challenge, many healthcare facilities do not regularly update or rehearse their emergency plans. When emergencies occur, outdated plans, untested communication systems, and a lack of real-time situational awareness can turn a manageable situation into a catastrophic one.
Identity-Aware Mustering
Know exactly who is in the facility at any moment — staff, patients, visitors — and account for everyone during evacuation or shelter-in-place.
Mass Notification
Instructions reach the right people at the right time through mobile alerts, overhead systems, and direct integration with security operations.
Automatic Zone Lockdown
Paired with identity systems, platforms can automatically lock down specific zones and redirect traffic flow during an active incident.
Modern emergency mustering and mass notification technology directly address these gaps. Identity-aware mustering systems allow hospitals to know exactly who is in the facility at any given moment (staff, patients, and visitors), and to account for everyone during an evacuation or shelter-in-place event. Real-time location awareness enables security and clinical teams to coordinate movement, identify individuals who may need assistance, and verify that all personnel have reached designated assembly points.
Mass notification platforms ensure that instructions reach the right people at the right time through mobile alerts, overhead systems, and direct integration with security operations. When paired with identity and access management systems, these platforms can also automatically lock down specific zones, redirect traffic flow, and provide incident commanders with the contextual intelligence they need to make faster, better-informed decisions.
Emergency preparedness is not a once-a-year planning exercise. It is an operational capability that must be continuously maintained, tested, and supported by technology that provides real-time visibility and coordinated response.
Compliance, Reporting, and Regulatory Governance
Healthcare organizations operate under a complex web of regulatory requirements, from The Joint Commission and CMS Conditions of Participation to OSHA workplace safety standards, HIPAA data protection rules, and state-level security mandates.
Compliance is not optional. Failure to meet regulatory standards can result in fines, loss of accreditation, reputational damage, and in the worst cases, direct harm to patients and staff.
The Joint Commission
CMS Conditions of Participation
OSHA Workplace Safety
HIPAA Data Protection
State-Level Security Mandates
The challenge for many hospitals is that compliance and reporting processes are manual, fragmented, and reactive. Security incident data lives in one system, access logs in another, visitor records in a third, and training documentation in a fourth. When auditors or regulators request evidence of policy enforcement, incident response, or access governance, security teams spend significant time assembling information from disconnected sources.
Integrated security platforms simplify compliance by centralizing identity data, access logs, incident records, and policy enforcement into a single system. Automated reporting reduces the burden on security teams and ensures that compliance evidence is always current, complete, and accessible.
More importantly, a unified platform shifts compliance from a retrospective reporting exercise into a continuous governance capability, where policies are enforced in real time, deviations are detected automatically, and corrective actions are triggered before they become audit findings.
The Convergence of Cyber and Physical Security — and the IT Access Gap
While this guide focuses primarily on physical security, it is increasingly impossible to separate physical and cyber risk in healthcare environments. Cyberattacks are no longer limited to data breaches targeting electronic health records. Attackers are now targeting the operational technology (OT) systems that control HVAC, fire alarms, access control infrastructure, medical devices, and building management systems.
A successful attack on these systems could disable access controls across a hospital, shut down environmental monitoring in operating rooms, disrupt fire suppression and alarm systems, or compromise the network infrastructure that security platforms depend on.
But the convergence problem runs deeper than OT vulnerability. In most hospitals, physical access and IT access are governed by entirely separate systems, separate teams, and separate processes. A clinician’s badge access to the maternity ward is managed by the security department, while their login credentials for the EHR system, pharmacy applications, and clinical databases are managed by IT. These two worlds rarely communicate.
The Problem: Siloed Governance
- Physical badge access managed by security
- IT credentials managed by a separate team
- Employee leaves — badge revoked, network login persists
- Contractor deactivated physically but active digitally
- Attack vectors exploited across both domains
The Solution: Converged Identity
- Single identity lifecycle from hire to termination
- Physical and digital access governed together
- Revocation happens simultaneously across all systems
- Role-based provisioning automated on day one
- Unified compliance history across physical + digital
This creates critical blind spots. When an employee transfers departments or leaves the organization, their physical access may be revoked while their IT credentials remain active, or vice versa. When a contractor’s engagement ends, their badge may be deactivated while their network login persists. These gaps are not theoretical, they are the exact attack vectors that threat actors exploit, and they exist because identity governance is fragmented across physical and digital domains.
Healthcare security leaders must treat physical and cyber access as a single, enterprise-wide identity problem. This means unifying the governance of who can enter which physical spaces with who can access which digital systems, applications, and data, all driven by the same identity lifecycle.
This is what converged identity and access management enables. Rather than managing physical badges in one system and IT credentials in another, hospitals can govern the complete access lifecycle from hire to role change to termination, across both domains simultaneously. Access is provisioned based on identity attributes and role, enforced through automated policies, and revoked immediately across all systems when roles change or engagements end.
The operational benefits extend beyond security. Automated provisioning eliminates the manual, error-prone processes that delay new hires from getting the access they need on day one. Self-service access requests reduce the administrative burden on both IT and security teams. And built-in compliance reporting for frameworks like HIPAA, Joint Commission, and CMS requirements, ensures that audits are backed by a complete, unified access history across physical and digital systems.
Maintaining Patient and Family Experience
While security is critical, hospitals must also maintain positive patient and family experiences. Overly restrictive or cumbersome security measures, long check-in lines, confusing visitor policies, and aggressive screening procedures, can create frustration and anxiety for people who are already in difficult situations.
The best healthcare security strategies are invisible to the people they protect. They operate in the background, verifying identities, enforcing access policies, and monitoring for risk without creating friction in the care delivery experience.
Modern visitor identity management systems achieve this by streamlining check-in processes, reducing lobby wait times through pre-registration workflows, and automating policy enforcement so that visitors experience a smooth, welcoming arrival while security protocols are rigorously followed behind the scenes.
The goal is not to choose between security and experience, it is to build systems where both are achieved simultaneously.
Conclusion
From Fragmentation to Control: Building a Unified Healthcare Security Strategy
Healthcare environments differ significantly from corporate offices, manufacturing facilities, or retail operations. The nature of care delivery itself creates a uniquely challenging security landscape.
Hospitals must remain accessible to patients, families, emergency responders, clinicians, students, contractors, vendors, and volunteers around the clock. Unlike a corporate campus where access can be strictly controlled, hospitals are fundamentally open environments serving diverse, unpredictable populations.
Security teams must manage a wide and overlapping range of risks.
Identity is the common thread across every challenge
Know who is in your facility
Assess risk before granting access
Control where individuals can go
Detect behavioral anomalies in real time
Intervene before situations escalate
When hospitals know who is in their facilities, every patient, visitor, employee, contractor, and vendor, they can assess risk before granting access. When they control where individuals can go based on verified identity and purpose, they limit exposure and reduce the likelihood of incidents. When they detect behavioral patterns and access anomalies in real time, they can intervene before situations escalate.
Achieving this level of control requires more than standalone tools. It requires a platform that brings together visitor management, workforce access governance, physical access control, security intelligence, and emergency response capabilities into a single, integrated system.
Platforms like Alert Enterprise Guardian bring together visitor identity management, workforce access governance (PIAM), and real-time security intelligence into a unified framework, allowing hospitals to manage every identity, enforce access policies consistently, detect risks with full context, and respond to incidents with speed and precision across the entire facility.
The result is a healthcare security strategy that protects healthcare workers, improves patient safety, strengthens operational resilience, and positions the organization for the evolving threats of 2026 and beyond.
Ready to unify your security?
See how Alert Enterprise Guardian brings visitor identity, workforce access governance, and real-time security intelligence into one platform.