Something big is coming to ISC West Booth #13115
In a world increasingly reliant on information, data centers have become the operational nerve center of the enterprise. Managing physical and logical access to data centers both is key to delivering enhanced security.
Data center security solutions from Alert Enterprise manage all categories of identities including employees, contractors, vendors, and visitors. With Alert Enterprise, global enterprises can apply a standard set of security policies across all their data centers making sure that all data is safe and company-wide operational integrity is maintained.
Seamless integration with HR Systems and Contractor Databases supports automated security policies requiring employees and contractors to submit access requests in advance and complete required training via Learning Management Systems. Contractors can enroll their staff ahead of time for pre-approval allowing the enterprise to enforce strict no drop-in or no-ad-hoc approval policies.
Visitor Management software pre-integrated with Physical Access Control Systems (PACS) extends the same level of protection for visitors, enforcing request approval before granting access through the enterprise-class workflow engine.
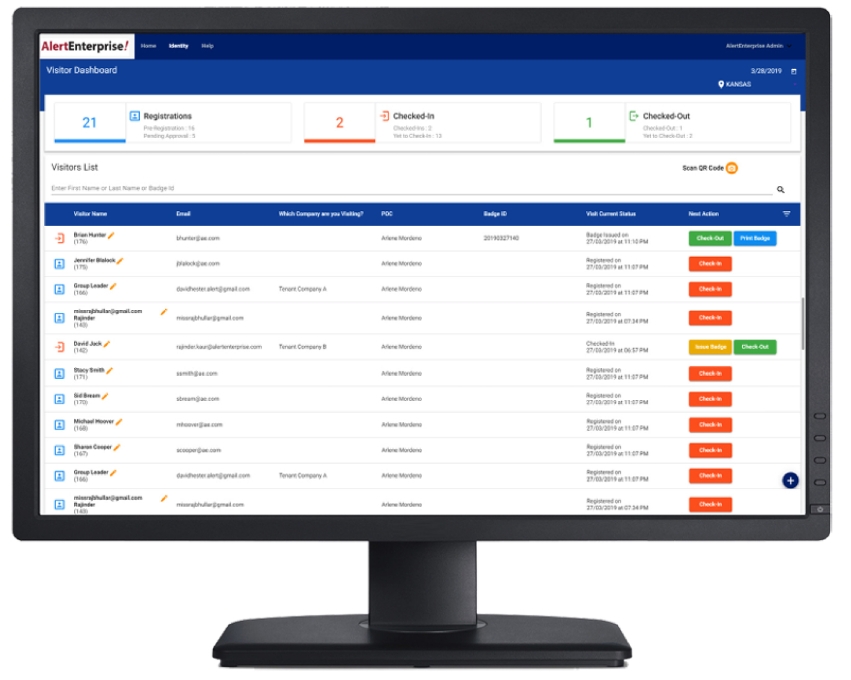
The Alert Enterprise Data Center Visitor / Contractor Management Solution’s browser-based interface enables convenient pre-visit enrollment and approval. Employee, contractor, vendor and visitor identities are automatically tracked against rules-based policies ensuring that only approved individuals are given access to the most critical infrastructure assets and areas within the enterprise. Automatic logging, time-stamping and approval flows can be accessed later for audit and compliance purposes.
Alert Enterprise Visitor Management Kiosk software with facial recognition technology delivers frictionless security to organizations that are looking to improve security and enhance customer experience with a powerful first impression at check-in. The new facial recognition feature provides fast and accurate on-site identity verification and makes it easy for an organization to add facial image analysis to the check-in process for employees, visitors, contractors, and guests arriving on-site.
At Alert Enterprise, trust is at the center of everything we do. We bring people, processes, data and technology together in true security convergence.
Subscribe to our newsletter:
Subscribe to our newsletter: